This article lists examples demonstrating practical use cases for taking action on Fortigate servers
Add Host to Group (Fortigate)
The below configuration allows you to connect to the FortiGate host and run any command
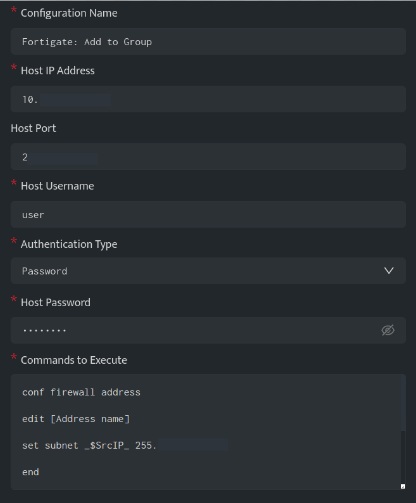
In the above configuration, execute the following commands
conf firewall address
edit [Address name]
set subnet _$SrcIP_ 255.255.255.255
end
conf firewall addrgrp
edit [Address group name]
append member [Address name]
end
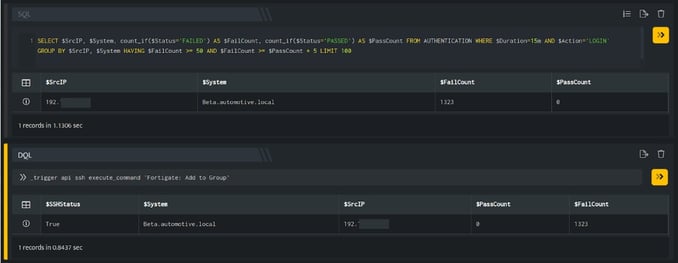
In the above figure, a search query is executed that displays all the suspicious IP Addresses that have failed at their login attempts more than 50 times. Using _trigger query, an API call is made to the above ssh integration configuration, which will add the IP Addresses in the $SrcIP column to the group mentioned in the configuration.
You need to apply the firewall rules to block the IP Addresses present in the group.
The below configuration allows you to connect to the FortiGate host and run any command
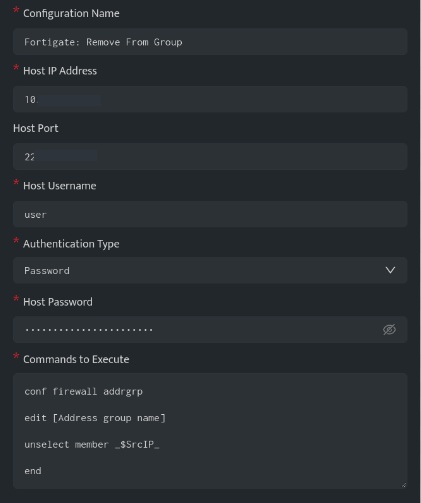
In the above configuration, execute the following commands
conf firewall addrgrp
edit [Address group name]
unselect member _$SrcIP_
end
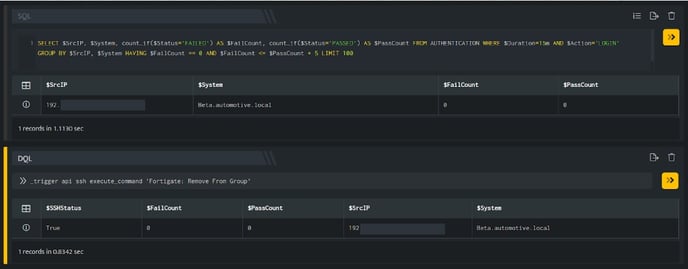
In the above figure, a search query is executed that displays all the IP Addresses that do not have any failed login attempts. Using _trigger query, an API call is made to the above ssh integration configuration, which will remove the IP Addresses in the $SrcIP column from the group mentioned in the configuration.
